HowTo Use The NST Network Tools Widgets: Difference between revisions
| Line 47: | Line 47: | ||
= MAC Address Tools = | = MAC Address Tools = | ||
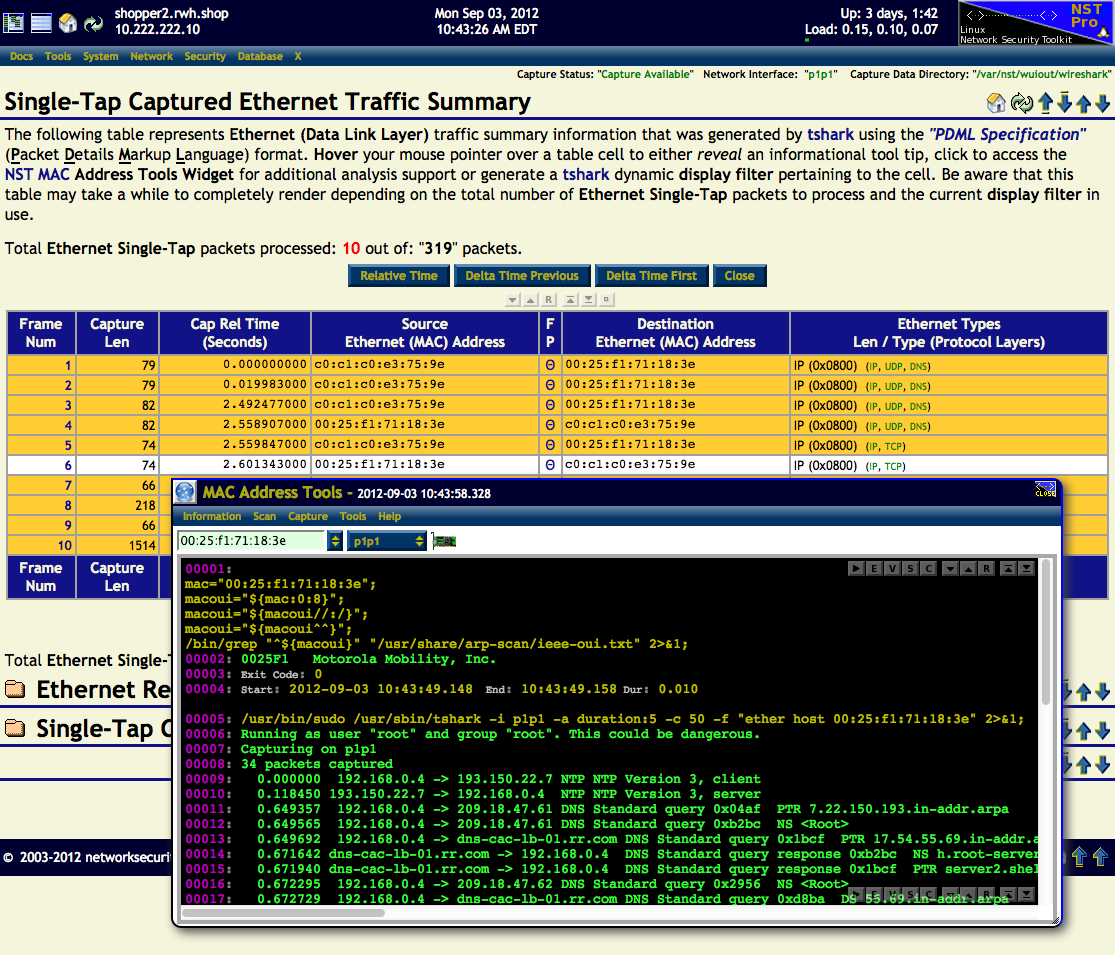
A use case example of the '''MAC Address Tools''' widget is shown in action below. The | A use case example of the '''MAC Address Tools''' widget is shown in action below. The Source Ethernet (MAC) Address: "'''00:25:f1:71:18:3e'''" for Frame Number: "'''6'''" found on this '''Single-Tap Captured Ethernet Traffic Summary''' page was ''clicked'' on. The '''MAC Address Tools''' widget was then popped up with this address shown. | ||
Firstly, a [http://en.wikipedia.org/wiki/Organizationally_Unique_Identifier '''OUI'''] lookup from the [http://en.wikipedia.org/wiki/Institute_of_Electrical_and_Electronics_Engineers '''IEEE'''] '''OUI NST''' text file: "'''/usr/share/arp-scan/ieee-oui.txt'''" (Menu: ''Information'' => ''OUI Lookup'') was performed. Secondly, a quick capture using the [http://en.wikipedia.org/wiki/Wireshark '''tshark'''] protocol analyzer (Menu: ''Capture'' => ''Quick'') was used to capture packets to and from this '''ether host''' address. | Firstly, a [http://en.wikipedia.org/wiki/Organizationally_Unique_Identifier '''OUI'''] lookup from the [http://en.wikipedia.org/wiki/Institute_of_Electrical_and_Electronics_Engineers '''IEEE'''] '''OUI NST''' text file: "'''/usr/share/arp-scan/ieee-oui.txt'''" (Menu: ''Information'' => ''OUI Lookup'') was performed. Secondly, a quick capture using the [http://en.wikipedia.org/wiki/Wireshark '''tshark'''] protocol analyzer (Menu: ''Capture'' => ''Quick'') was used to capture packets to and from this '''ether host''' address. | ||
Revision as of 10:17, 3 September 2012
Overview
The NST WUI includes pop-up network tools widgets for IPv4, IPv6, Host Names, and MAC addresses. Each NST WUI pages which display network addresses or host names will allow you to click on the network entity to bring up the appropriate network tools widget. Once the widget is displayed, you can perform a variety of related actions using the network entity. See the NST Shell Console Command Reference Page for supporting information.
Each tools widgets has a collection of specific predefined actions that can be executed. An NST Shell Console output area is attached and used for action results. An NST Shell Console Editor is also available for command replay and option modifications.
Other network tools widgets for setting DNS overrides globally or for each network interface and a [CloudShark Upload Manager] are available.
IPv4 Address Tools
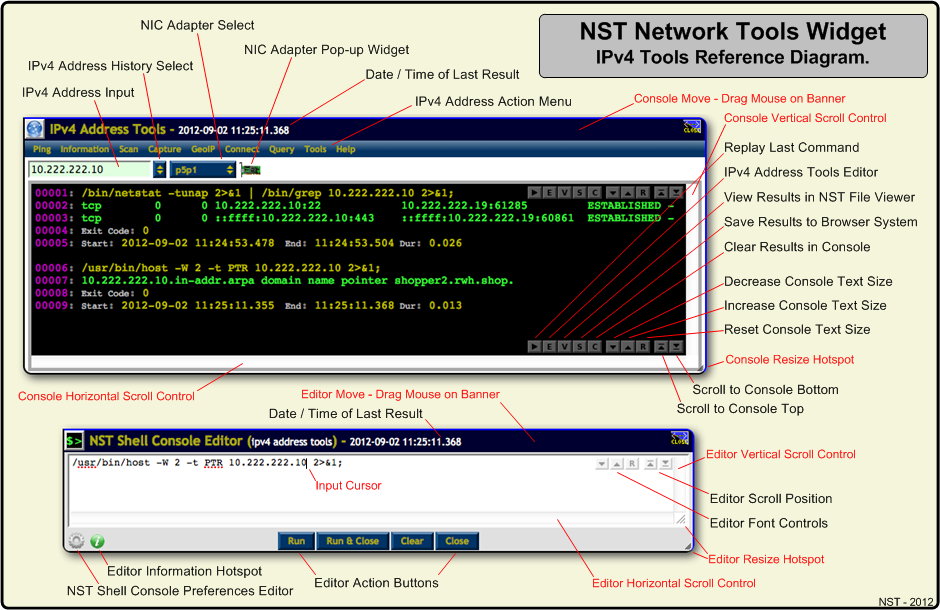
The image below serves as a reference for the IPv4 Address Network Tools Widget. Common controls can be similarly found on all other NST Network Tools Widgets. Clicking on most IPv4 addresses throughout the NST WUI will bring up this tools widget with the IPv4 address populated in the input field and ready for an action to be performed using it. The IPv4 address will be added to your browser session store so that it may be used and selected at a later time with the IPv4 Address History Select button.
One can also bring up the IPv4 Address Tools widget through the NST Navigation Menu (i.e. Tools => Network Widgets => IPv4 Address).
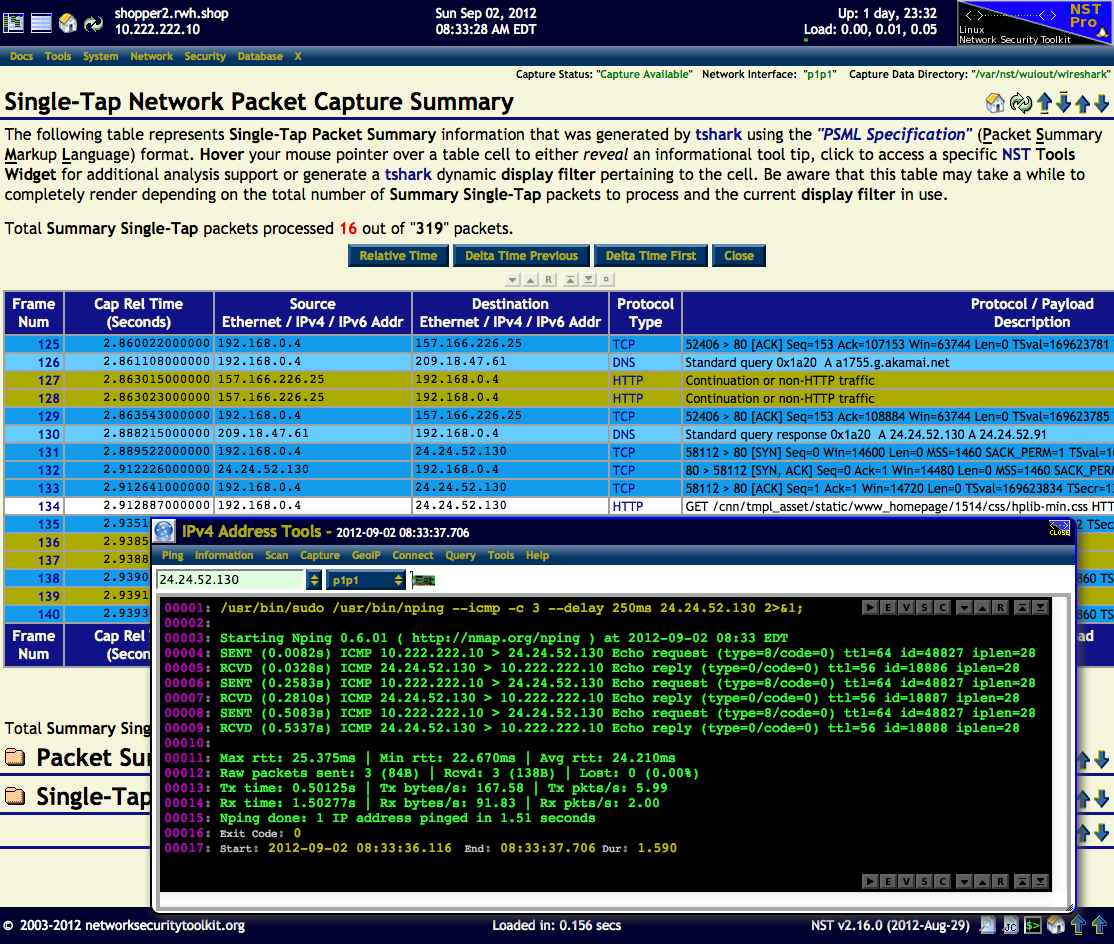
A use case example of the IPv4 Address Tools widget is shown in action below. The Destination IPv4 Address: "24.24.52.130" for Frame Number: "134" found on this Single-Tap Network Packet Capture Summary page was clicked on. The IPv4 Address Tools widget was then popped up with this address shown.
In this example the Nmap Network packet generation tool / ping utility (Menu: Ping) was then executed.
IPv6 Address Tools
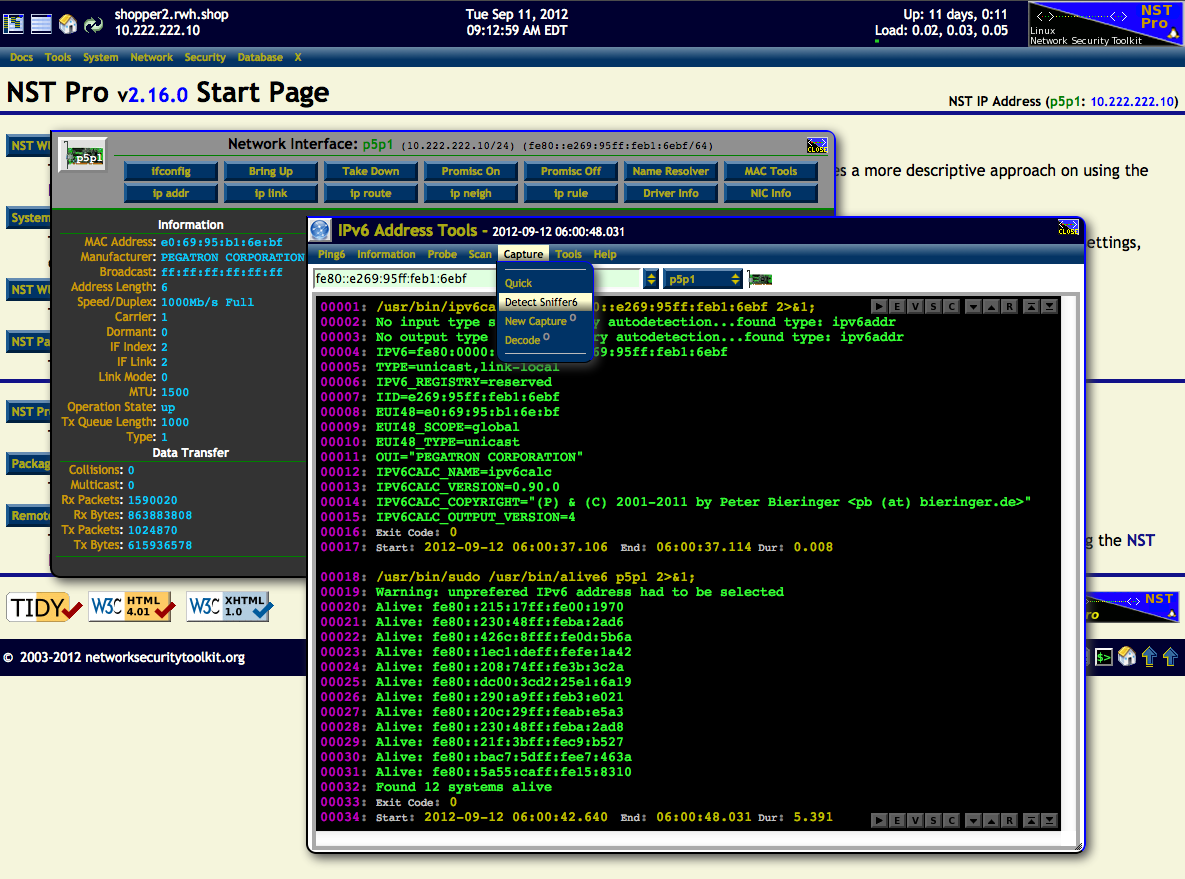
In this use case, the IPv6 Address Tools widget will be demonstrated. The p5p1 network interface label to the right of the "NST IP Address" on the NST Start Page was first clicked on. This popped up the NIC Adapter widget for the p5p1 network interface. The IPv6 Address: "fe80::e269:95ff:feb1:6ebf" located on the NIC Adapter widget top banner was then clicked on. This revealed the IPv6 Address Tools widget.
Firstly, the ipv6calc utility (Menu: Information => IPv6Calc) was used to show information about the IPv6 address. Secondly, the alive6 network utility (Menu: Scan => Alive6) was used to show all active and responding IPv6 addresses on the network segment for the selected interface: p5p1.
One can also bring up the IPv6 Address Tools widget through the NST Navigation Menu (i.e. Tools => Network Widgets => IPv6 Address).
Host Name Tools
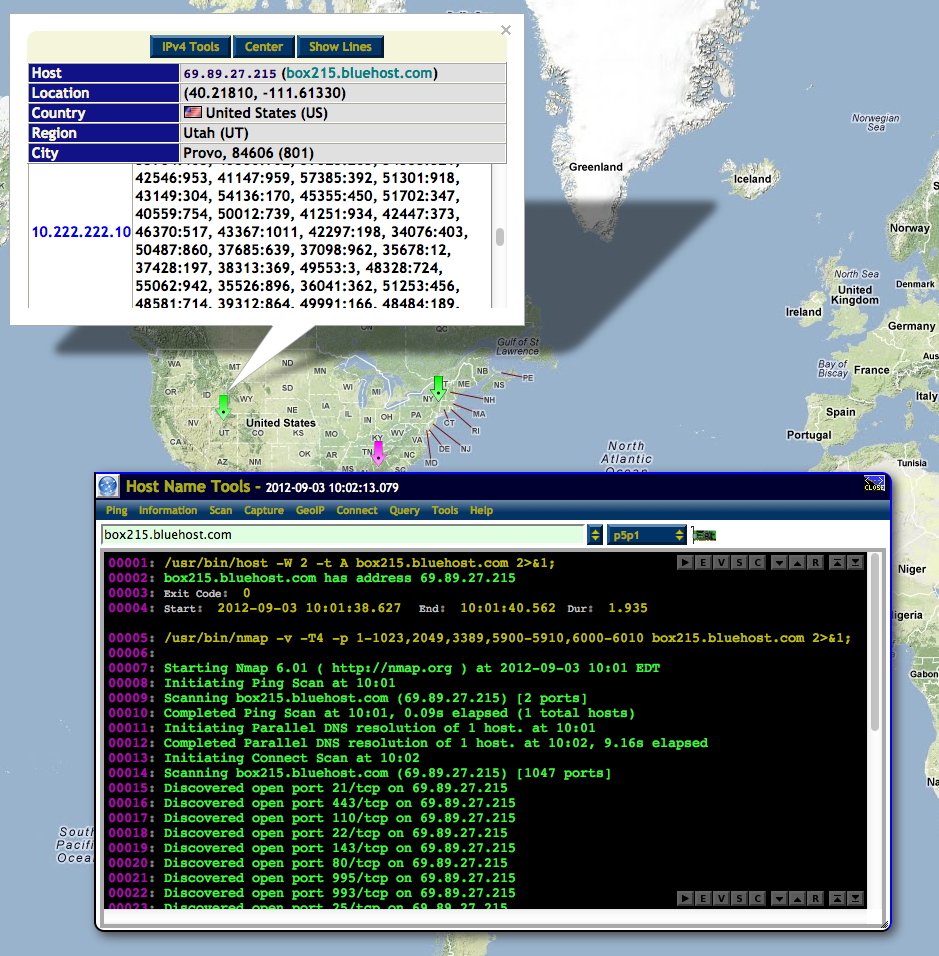
In this use case, the Host Name Tools widget will be featured. The Active Connections Monitor (Menu: Network => Monitors => Active Connections) will be used to reveal the Host Name Tools widget. In this example, the green host map marker found in the state of Utah, USA was clicked on. This popped up an information window for this host. The associated fully qualified host domain name: "box215.bluehost.com" was then clicked on to bring up the Host Name Tools widget.
Firstly, the host utility (Menu: Information => Lookup IP) was used to lookup the IPv4 address for this host name. Secondly, the Nmap network utility (Menu: Scan => Nmap TCP) was used to discover all active TCP/IP open ports on this host.
One can also bring up the Host Name Tools widget through the NST Navigation Menu (i.e. Tools => Network Widgets => Host Name).
MAC Address Tools
A use case example of the MAC Address Tools widget is shown in action below. The Source Ethernet (MAC) Address: "00:25:f1:71:18:3e" for Frame Number: "6" found on this Single-Tap Captured Ethernet Traffic Summary page was clicked on. The MAC Address Tools widget was then popped up with this address shown.
Firstly, a OUI lookup from the IEEE OUI NST text file: "/usr/share/arp-scan/ieee-oui.txt" (Menu: Information => OUI Lookup) was performed. Secondly, a quick capture using the tshark protocol analyzer (Menu: Capture => Quick) was used to capture packets to and from this ether host address.